Problem
I want to configure a roaming IPsec client/server setup where I can can connect to the firewall VPN server from the Internet but also from inside/behind the firewall. But when i try to connect with the client from the inside nothing happens, the firewall does not reply at all.
Solution
The firewall behaves this way because the IPsec engine expects that the interface where the request was received will be the sending interface as well. But if you connect to , for example, the WAN interface from the LAN interface, it will be LAN that will be the sending interface towards the client.
The solution to this problem is straightforward. Configure the Local Endpoint setting on the IPsec tunnel to be the IP address of the external interface, as shown in the screenshot below:
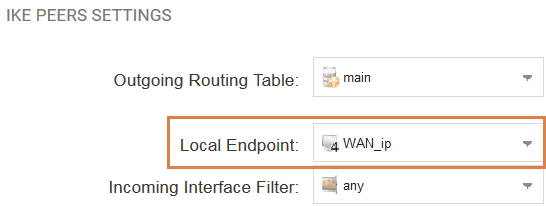
Now, the IPsec engine and cOS Core will know which IP address it should use as the sender IP even if the sender interface is the internal LAN interface.
Note: In older cOS Core versions where the Local Endpoint setting does not exist, the solution is to set the same IP address on both WAN and LAN interface.
Related articles
11 Jan, 2023 ipsec core vpn
24 Mar, 2023 core ipsec ippool dhcp
12 Apr, 2023 core proxyarp arp ipsec routing
18 Mar, 2024 core certificate oneconnect ipsec vpn
1 Jun, 2026 vpn core ipsec alg highavailability trafficshaping
23 Nov, 2022 core ipsec
21 Feb, 2023 ipsec certificate windows ca core
22 Mar, 2021 core ipsec routing
18 Mar, 2024 core incontrol certificate oneconnect ipsec vpn
11 Dec, 2025 core routing ospf ipsec
17 Jun, 2021 core ipsec routing
8 Mar, 2023 core l2tp ipsec
20 Feb, 2023 core vpn ipsec
4 Aug, 2023 core ipsec troubleshoot ike
14 Apr, 2021 core license ipsec
8 Sep, 2020 core ipsec rules access
29 Mar, 2023 ipsec core windows vpn l2tp
16 Sep, 2020 vpn ipsec ikev2 windows howto dh
7 Dec, 2022 ipsec ike troubleshoot core
14 Dec, 2022 core ipsec
5 Apr, 2023 core nps ipsec radius legacy
14 Mar, 2023 core ipsec vpn ikev2 certificate
23 Aug, 2022 core ipsec license memory
15 Mar, 2023 core ipsec ipv6
23 Aug, 2022 core connections ipsec memory
13 Feb, 2023 ipsec core routing failover
28 Mar, 2023 dhcp ipsec core