What is a certificate authority (CA)?
A certificate authority (CA) is a trusted entity that issues certificates to other entities. The CA digitally signs all certificates it issues. A valid CA signature in a certificate verifies the identity of the certificate holder, and guarantees that the certificate has not been tampered with by any third party.
A CA is responsible for making sure that the information in every certificate it issues is correct. It also has to make sure that the identity of the certificate matches the identity of the certificate holder.
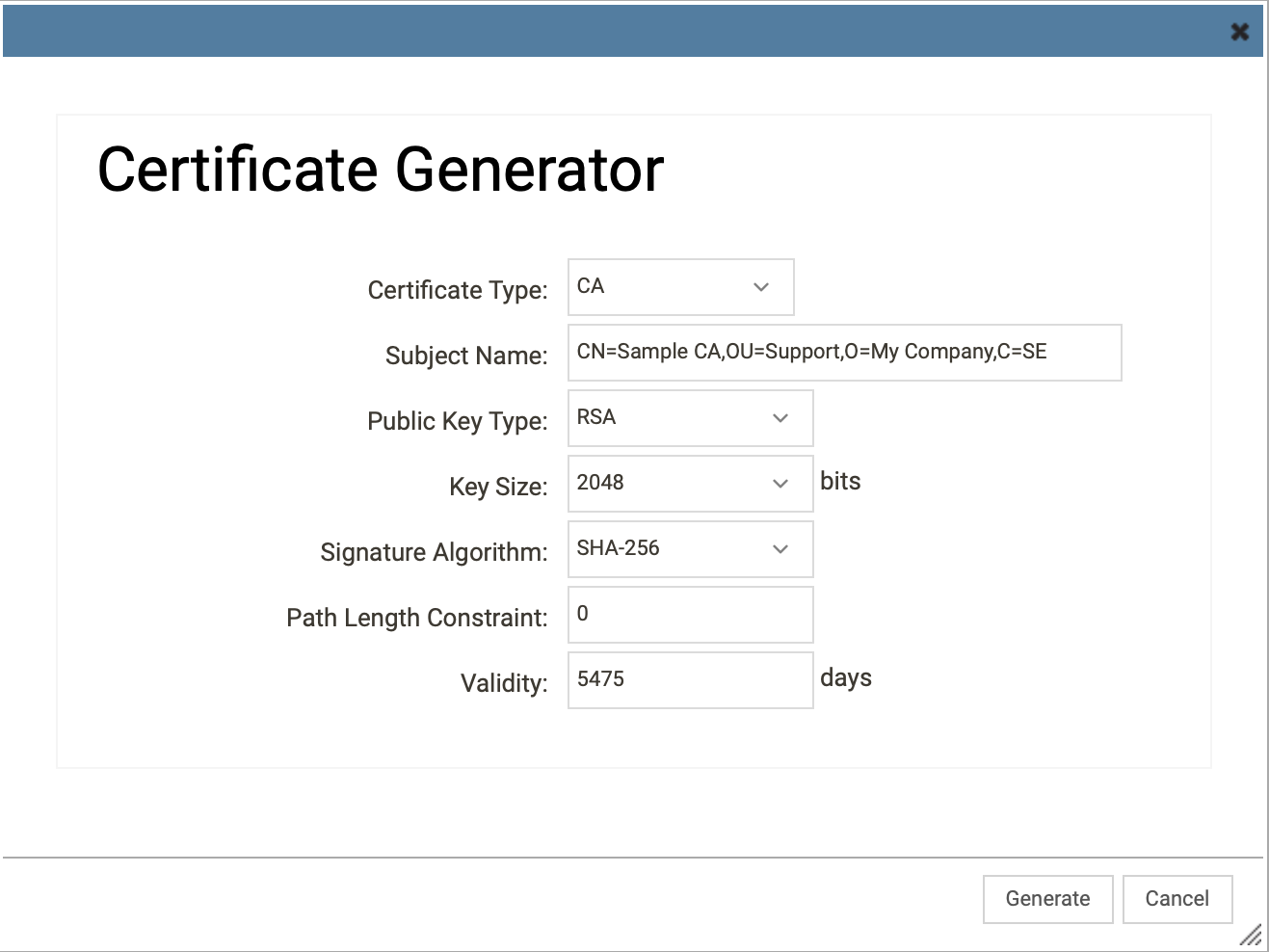
Creating the CA certificate
To create a CA certificate browse to Key Ring (Objects → Key Ring) and add a new certificate, give it a name and click on the Configure button to configure the CA certificate.
The following Subject Name fields can be configured on a CA certifcate:
- CN: CommonName
- OU: OrganizationalUnit
- O: Organization
- L: Locality
- C: CountryName
Example: CN=Sample CA,OU=Support,O=My Company,C=SE
The Public Key Type can be either RSA or EC (Elliptic Curves), if using EC make sure the Key Size is 384 or higher, also note that RSA certificates have more compatibility, especially around IPsec, but EC certificates are consider faster and more secure. If the certificate will only be used for HTTPS based features, pick EC, if also going to be used for IPsec then select RSA.
Example below:
When generated there should be a certificate looking something like this:
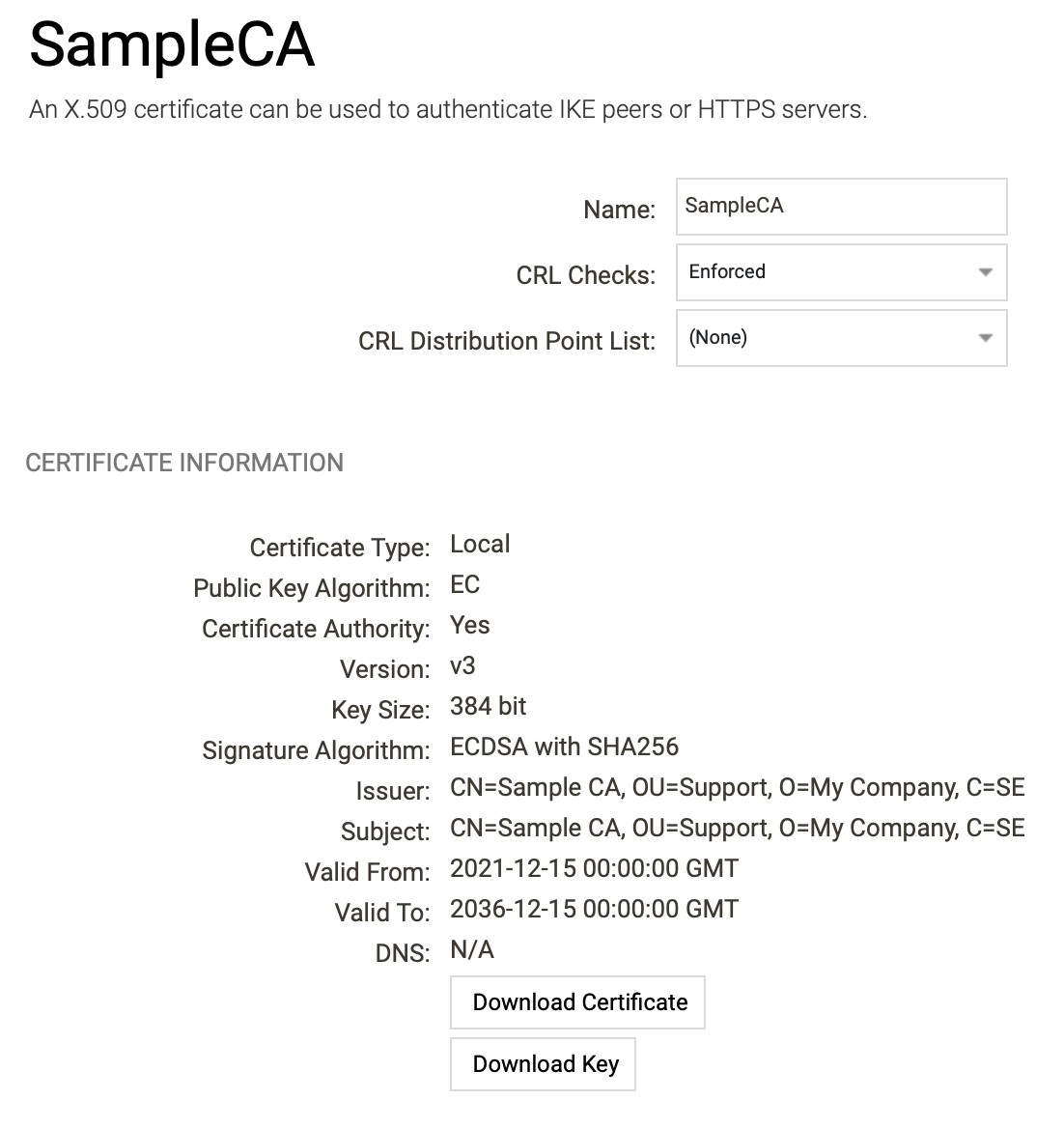
Download this Certificate and import into trusted CA Store on end devices.
Download the certificate (not the key) and deploy it to your end devices so they will trust certificates issued by the CA, this can be done in a number of ways depending on operating system or if the device is managed by a device management system.
Example: Creating a CA signed End-Entity certificate for OneConnect and/or WebUI
To create a a signed End-Entity certificate browse to Key Ring (Objects → Key Ring) and add a new certificate, give it a name and click on the Configure button to configure the End-Entity certificate.
Make sure End-Entity is selected and the CA Certificate created in the previous step is selected as Issuer Certificate.
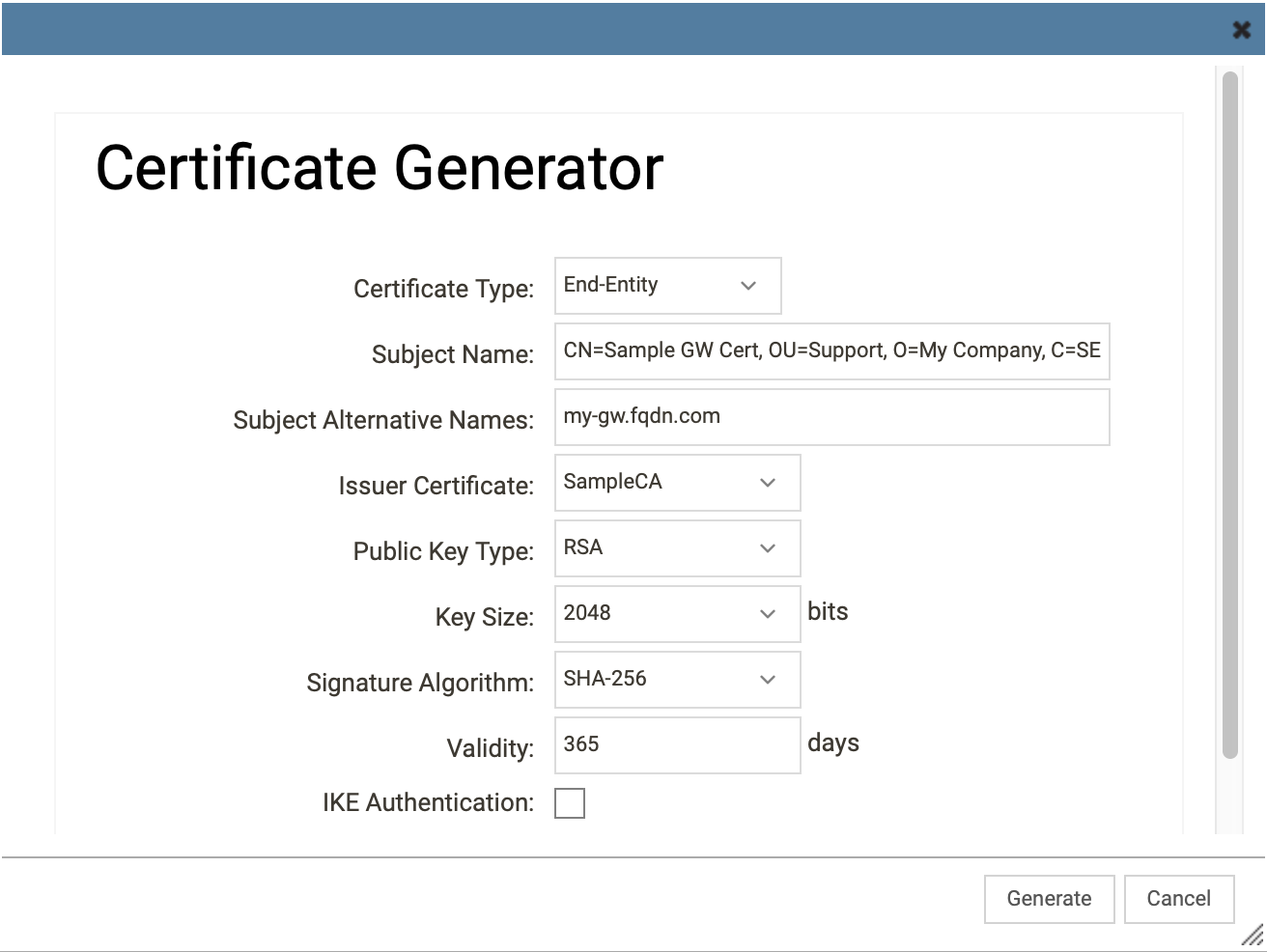
Note: The Subject Alternative Name (SAN) of the certificate should be the hostname entered and used to connect to the WebUI and/or the OneConnect interface in cOS Core.
Note: Validity should not be to long on End-Identity certificates.
Note: Key Size must be 384 bits or higher if using EC.
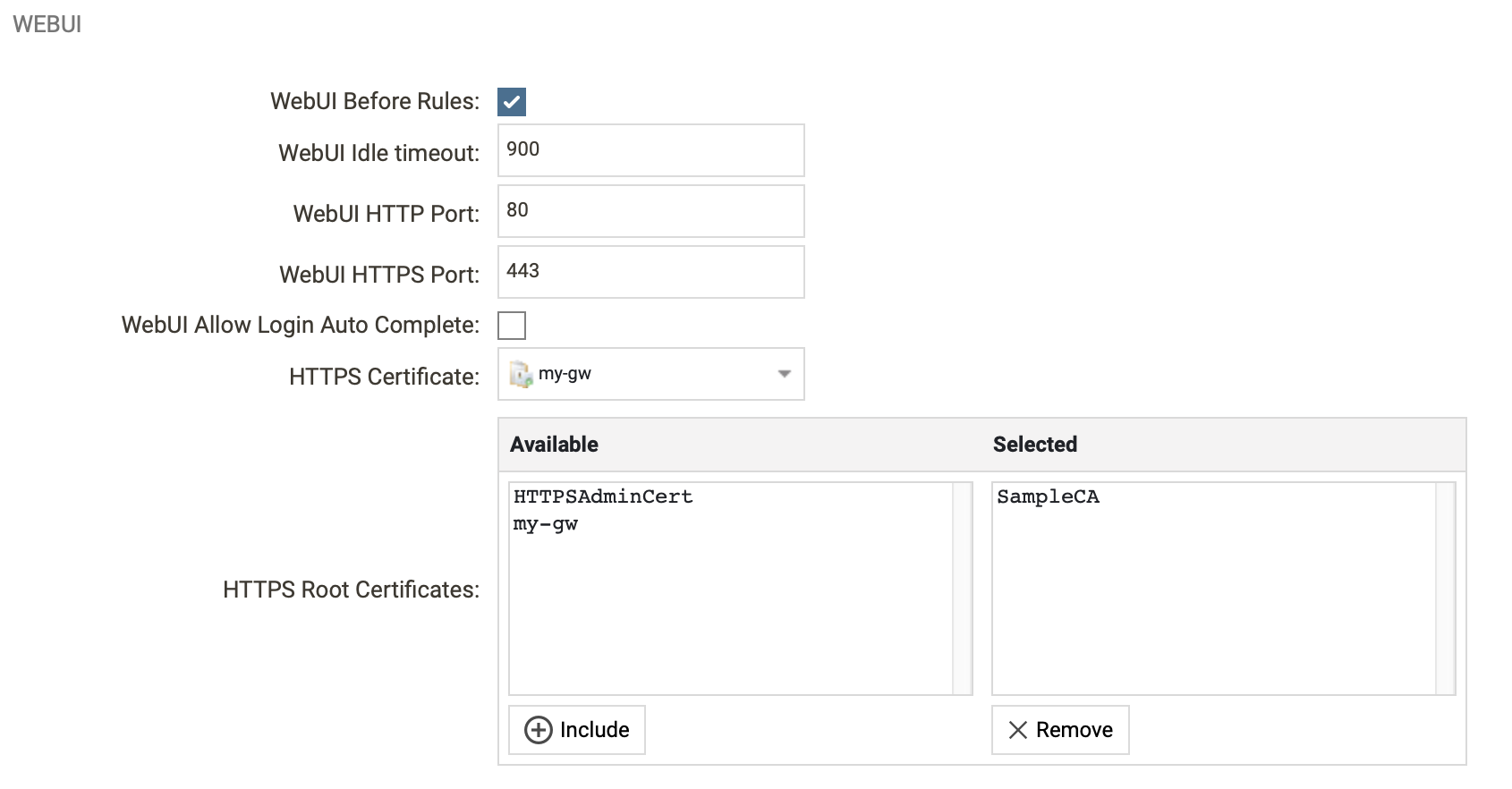
Configure NetWall to use the certificate
To use the newly created certificate go to Advanced Settings in Remote Management (Device Settings → Remote Settings → Advanced Settings) and scroll down to the WebUI settings.
Select the created certificate as HTTPS Certificate and the CA Certificate as HTTPS Root Certificate.
Related articles
11 Jan, 2023 ipsec core vpn
10 Mar, 2023 core vpn ikev2 windows radius certificate
13 Jun, 2022 oneconnect macos ios windows android
3 Jun, 2022 oneconnect openconnect sslvpn
8 Feb, 2026 oneconnect sase cloud
28 Mar, 2023 ikev2 windows vpn routing splittunneling
8 Feb, 2026 oneconnect sase
28 Apr, 2023 openconnect oneconnect macos ios iphone
18 Mar, 2024 core certificate oneconnect ipsec vpn
6 Dec, 2025 sase cloud oidc oneconnect core
23 Aug, 2022 sslvpn openconnect oneconnect android core
29 Oct, 2021 sslvpn openconnect oneconnect windows
9 Feb, 2024 core oneconnect windows splittunneling dns
18 Mar, 2024 core incontrol certificate oneconnect ipsec vpn
27 Oct, 2022 oneconnect log
5 Mar, 2021 sslvpn openconnect oneconnect linux core
8 Apr, 2021 core sslvpn oneconnect interfaces arp
4 Jul, 2025 core oneconnect oidc
18 Mar, 2024 onetouch sslvpn oneconnect troubleshoot certificate
20 Feb, 2023 core vpn ipsec
25 Feb, 2022 oneconnect windows howto
29 Mar, 2023 ipsec core windows vpn l2tp
8 Feb, 2026 sase oneconnect core userauth oidc
19 May, 2026 oneconnect core sase
27 Feb, 2024 oneconnect userbased core
23 Aug, 2022 core oneconnect
28 Nov, 2022 core configuration oneconnect
21 Nov, 2025 oneconnect sase cloud radius
16 Sep, 2020 vpn ipsec ikev2 windows howto dh
14 Mar, 2023 core ipsec vpn ikev2 certificate
11 May, 2023 oneconnect certificate howto
27 Aug, 2024 oneconnect windows
22 May, 2024 netwall ikev2 windows certificate vpn core
8 Jun, 2022 openconnect oneconnect android
23 Aug, 2022 sslvpn openconnect oneconnect macos windows linux core