What is OpenConnect-GUI?
OpenConnect-GUI is a third party client compatible with a OneConnect Interface in Clavister cOS Core. It can be found at https://openconnect.github.io/openconnect-gui/. OpenConnect-GUI can be downloaded as pre-compiled binaries for both Windows and macOS. As for Linux and other Unix-like operating systems, it can be compiled from source or installed via the OS package manager. The MacOS interface is used as an example below but Windows is configured similarly.
Configuring OpenConnect-GUI
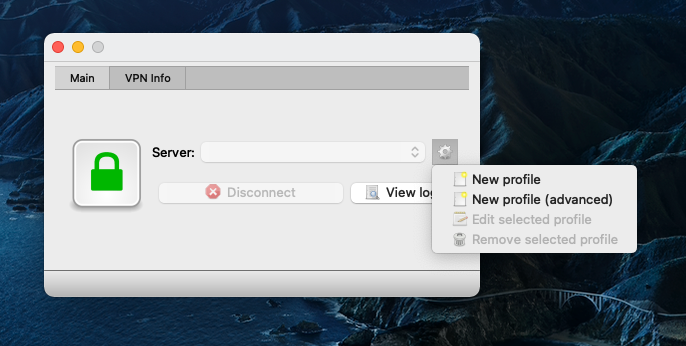
Start OpenConnect-GUI. The example below shows the client running under macOS. Click the cogwheel and select New profile.
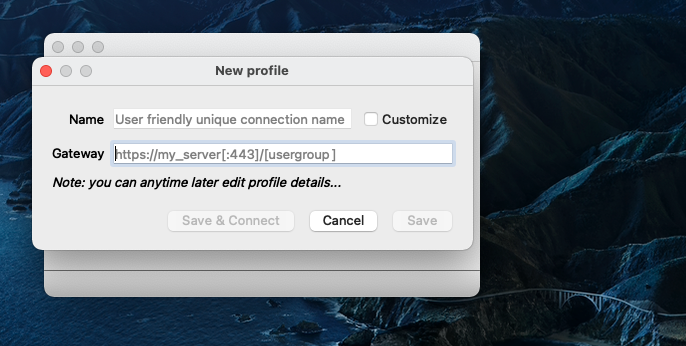
As Gateway enter the full url (for example https://myvpn.mydomain.tld) as configured in the OneConnect interface in cOS Core (hostname and server port if not 443) and click Save & Connect, Name is optional and will default to the same as Gateway if left blank.
Note: The hostname entered as Gateway must be the same as either the Common Name (CN) or one of the Subject Alternative Name (SAN) of the certificate used by the OneConnect Interface in cOS Core.
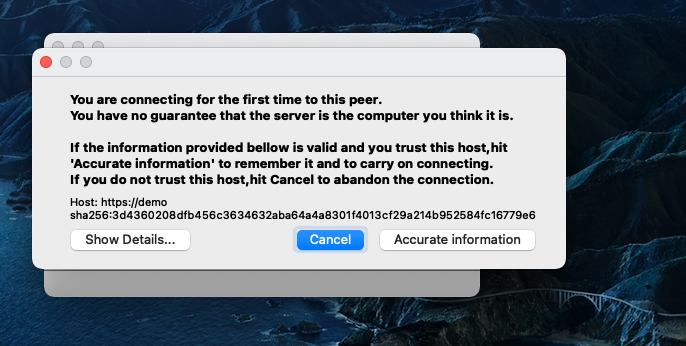
On initial connection, a pop-up to verify server certificate will appear. Click Show Details… to verify certificate. If everything looks okay, click Accurate information to proceed with the connection attempt.
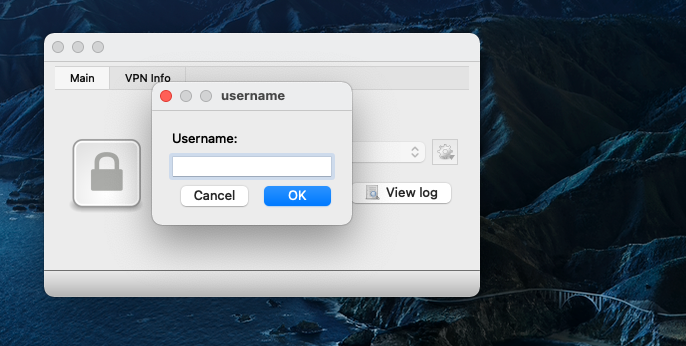
A pop-up to enter a username will be forwarded from cOS Core. If the connection is successful the username will be saved in the OpenConnect-GUI profile and will not be requested on subsequent connection attempts.
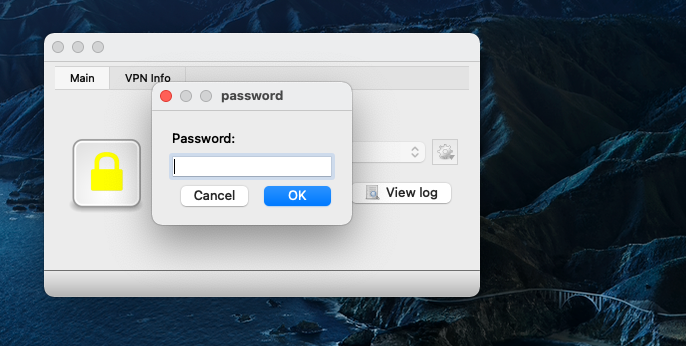
A separate pop-up for the password will be presented to the user.
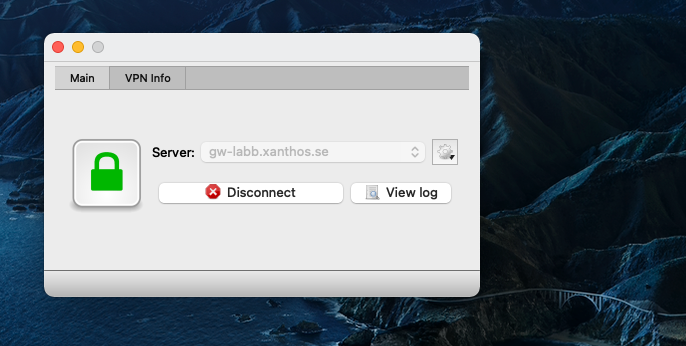
The pad-lock in OpenConnect-GUI will turn green when successfully connected.
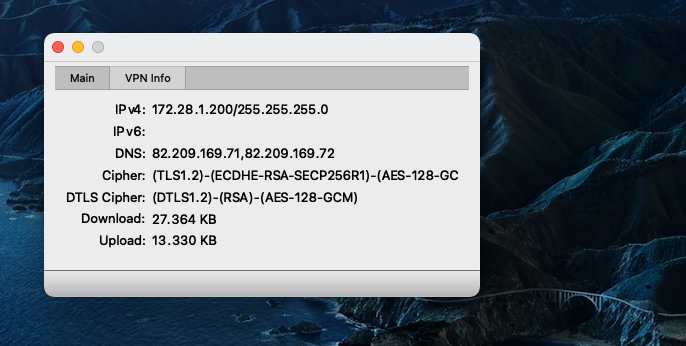
On the VPN Info tab detailed information about the SSL VPN tunnel can be seen, such as assigned IP, ciphers in use and if DTLS is active.
Related articles
11 Jan, 2023 ipsec core vpn
10 Mar, 2023 core vpn ikev2 windows radius certificate
28 Mar, 2023 ikev2 windows vpn routing splittunneling
18 Mar, 2024 core certificate oneconnect ipsec vpn
30 Mar, 2021 linux easyaccess
18 Mar, 2024 core incontrol certificate oneconnect ipsec vpn
5 Mar, 2021 sslvpn openconnect oneconnect linux core
20 Feb, 2023 core vpn ipsec
29 Mar, 2023 ipsec core windows vpn l2tp
16 Sep, 2020 vpn ipsec ikev2 windows howto dh
14 Mar, 2023 core ipsec vpn ikev2 certificate
22 May, 2024 netwall ikev2 windows certificate vpn core